With each passing year, hackers develop more sophisticated tools and programs to stay ahead of the curve and deal a lot of headaches to cybersecurity experts. But, one tool that has been around for decades and is still dangerous as it was when it was invented is a keylogger.
Keyloggers are notorious for their ability to collect all of your personal data without you even noticing it. They work quietly in the background, monitoring every word you type without giving any sign of their existence.
So, what’s keylogging, and how harmful can it be? More importantly, are there any reliable tips on how to detect keylogging and prevent keylogging attacks? In this guide, we’ll share the best ways to ensure keylogging protection and discuss valuable pointers on how to detect keylogging software.
What is Keylogging?
Before we talk about more complex aspects of keylogging, let’s start with the basics, beginning with the keylogging definition. If you’re wondering what does keylogging mean, this term can actually refer to two things.
Firstly, keylogging can refer to keystroke logging. This is the activity of keeping a detailed record of every key pressed on a keyboard. Besides that, it can also describe keylogger tools. These are devices or programs that are used to record these keystrokes.
In their nature, keyloggers can be used for legitimate research purposes. But, we mostly associate them with illegal or harmful activities in which malicious hackers exploit unsuspecting targets for profit.
How Does Keylogging Work?
Keyloggers can work differently depending on the way they are installed on the target device and the way they collect data. There are two types of keyloggers. These are:
- Hardware Keyloggers - such keyloggers can’t be detected by antivirus and antimalware software, as they aren’t installed on the computer. Instead, they use their own internal memory to store information. Hardware keyloggers are more challenging to set up as they require physical access to the target, for example, installing a fake keyboard overlay on an ATM.
- Software Keyloggers - these types of keyloggers are much more common as they are more discrete and can easily hide in your system. These keyloggers can reach your device on a Kernel level, on an API level, or even on a screen and browser level.
With this in mind, there are two main ways a keylogger can get on your device. A hardware keylogger has to be physically installed, while software keyloggers can infect your device remotely. Because of this, software keyloggers are often associated with malware. To be more precise, the most prevalent forms of keystroke malware include:
- Phishing Emails - you can accidentally download a keylogger by clicking on a link in a phishing email or text message.
- Viruses - cybercriminals often use Trojan viruses disguised as legitimate files or programs. Once you download and install them, the Trojan virus automatically starts keylogging your valuable information.
- Zero-day Exploits - these security breaches occur when attackers discover some inherent security flaws in a system or program before the developers. They use this to deliver the malware before developers discover the programming fault.
The Biggest Threats of Keyloggers
To look at this topic from a different perspective for a second, keyloggers can be used for completely legitimate purposes, as we mentioned before. You can intentionally download them or purchase them from a trusted platform to perform various research activities.
Some of the most common examples of legal keylogger use include IT troubleshooting, user experience monitoring, or company-wide data monitoring and exchange. You can even use keylogging tools to monitor and supervise your children’s online activity by setting parental controls.
Unfortunately, there are many more negative examples of keylogger use. Moreover, the threats of keyloggers are numerous and often very worrying. If cybercriminals manage to set up a keylogger on your device, they can see and record everything you type.
So, imagine just how much information they can collect by seeing your login credentials, emails, texts, and web browsing interests. After they steal your personal and sensitive information, they can exploit it for various criminal purposes.
For instance, cybercriminals can steal your identity, perform financial fraud in your name, use the collected data to ransom you, stalk you online, or perform many other nefarious misdeeds. This is why it’s crucial to learn how to prevent keylogging and learn how to detect whether you already have a keylogger installed on your device. This brings us to the next key point.
How to Detect Keylogging?
At this point, you’re probably worried by all of the potential dangers and disruptions keyloggers can cause you. This is certainly true, but luckily there are many practical things you can do to detect and remove keyloggers from your device. Here are some helpful steps you can take to detect and remove a keylogger:
The first thing you should do is run through the list of all software you have on your computer. Be thorough and observant, as some keyloggers can blend with other software or be similar in name, making them harder to detect.
Once you’ve found a suspicious program or file, remove or uninstall it. But, make sure to double-check, as even some programs that seem questionable might be necessary, so you should be certain that it’s not an essential tool before you delete it.
As we’ve mentioned briefly above, some keyloggers only focus on your browser, meaning that they only infect your device through browser extensions. Naturally, checking this is simpler than checking all of your software.
If you discover any unfamiliar sounding extensions or any extensions that you haven’t activated yourself, make sure to deactivate and remove them, as they could potentially be malicious.
Sometimes, even following the above steps won’t help you find any keylogging tools on your device. Plus, even if you find and remove some keyloggers, you can never be completely sure that you’ve got rid of all malicious software.
This is why the best safety measure for removing keyloggers from your device is to perform a factory reset of the device. That way, you will wipe all data from your device, including any harmful files and software.
How to Avoid Keylogging?
While it’s useful to know how to detect keylogging software it’s arguably more convenient to learn proper keylogging prevention practices. In this regard, here are some of the best tips on how to prevent yourself from keylogging:
- Avoid downloading files from unfamiliar sources
- Enable two-factor authentication
- Use a virtual keyboard
- Have a robust antivirus program
- Use voice-to-text instead of a keyboard
- Use a password manager
- Have a physical security key
Using a hardware security key and password manager like the Hideez Key ensures strong protection against keyloggers. As you will be eliminating the process of manually typing the information, the keyloggers won’t be able to record any of your login credentials or other valuable information.
All you have to do is pair your Hideez Key with your PC using Bluetooth or NFC and download the Hideez Client software for Windows. Then, you can import or add your login credentials for up to 1000 accounts. With this done, you’ll be able to autofill your account data, generate new strong passwords and even one-time passwords as your second factor.
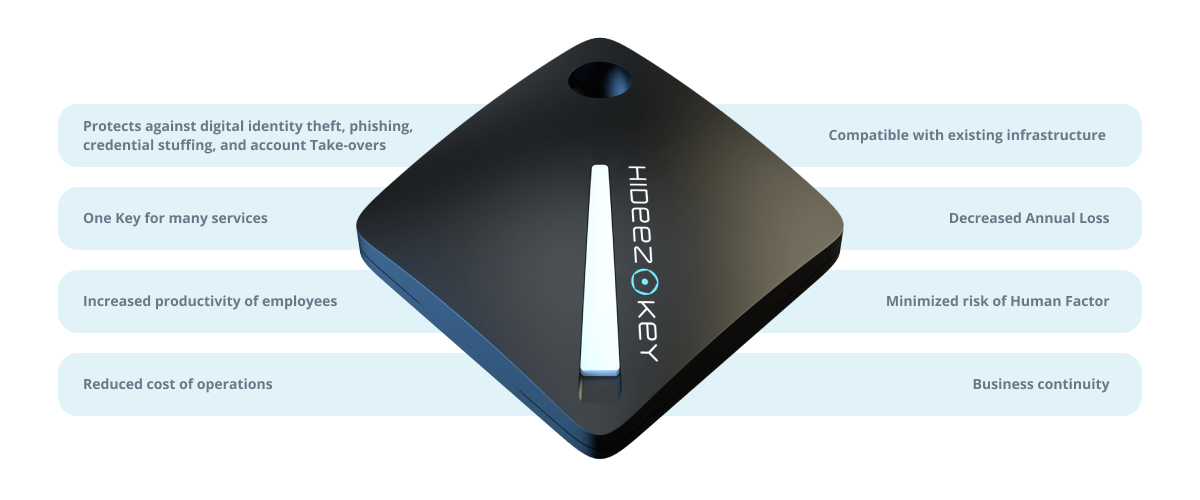
As a result, you will be protected against keylogging and other online threats like phishing, spoofing, and man-in-the-middle attacks. If you need a business version of this convenient and supersecure solution, we also offer an enterprise option in the form of the Hideez Authentication Service.
The benefits of using Hideez Keys:
- Hardware Password Manager - the Hideez Key works as an encrypted password manager with autofill. The key’s specific security architecture encrypts both the private and sensitive data and the communication channel itself.
- FIDO Security Key - Hideez Key is FIDO-certified, meaning that you can use it as your main verification factor on websites that support passwordless authentication and passwordless 2FA. This includes sites and services like Microsoft, Facebook, Google, and many more.
- Proximity Authentication - You can use the Hideez Key to lock or unlock your computer based on Bluetooth proximity when you get near the PC or walk away from it.
- RFID Key Fob - Lastly, you can program the key to open any one electronic door lock, enabling you more convenient access to your office, parking lot, or any other frequently used place.
If you want to protect your computer from keylogging malware, we’ve prepared special deals for you! Use the promo code TRYHIDEEZ at checkout to get a 10% discount when buying the Hideez Key for personal use. Moreover, if you’re looking for an enterprise solution, you can also schedule a personalized demo or request a free pilot by clicking the buttons below:

