Passwordless Access Control Solutions for Law Enforcement Agencies

Secure IT infrastructure with the power of secure passwordless solutions. Let onsite and remote employees access their accounts and workstations in seconds, without phishing threats or data breaches.
41%
Agencies deploy cybersecurity services
105 sec.
Average time police officers spend on authentication
30%
Agencies that have a cyber incident response plan
$7.13 Million
Average cost of a data breach
What is Passwordless Authentication?
How Will Your Organization Benefit From passwordless Authentication and MFA?
- Improved Security: Passwords can be stolen or cracked, leaving enterprise networks vulnerable to attacks. Replace traditional passwords with stronger, more secure sign-in methods, such as biometrics or security keys.
- Reduced IT Burden: Managing passwords is time-consuming and expensive for IT departments. Passwordless solutions eliminate the need to manage and reset passwords, freeing up IT resources for other tasks.
- Enhanced User Experience: Passwordless login streamlines the authentication process, making it more user-friendly. This, in turn, can improve employee productivity and satisfaction.
- Compliance: Passwordless auth provides stronger authentication measures, enabling organizations to comply with various regulatory requirements, such as GDPR, HIPAA, PCI DSS, and more.
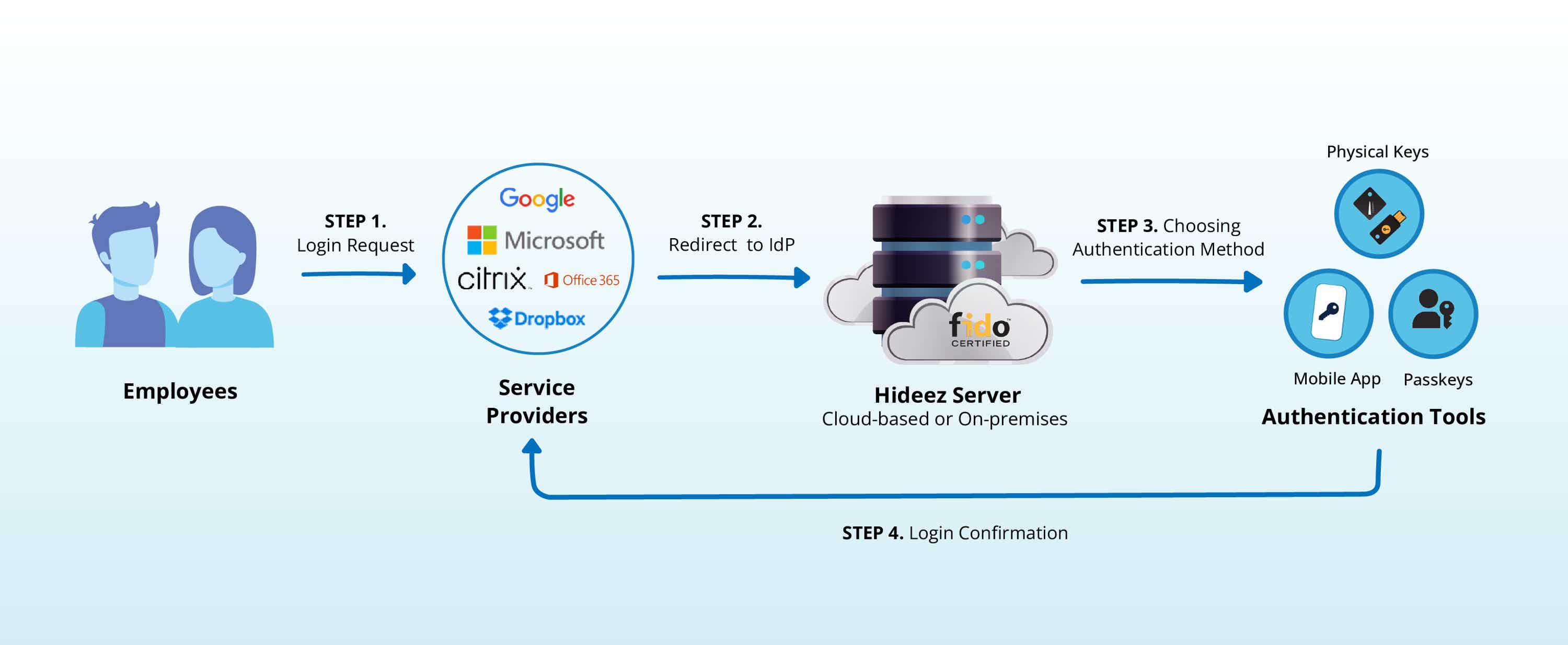
How Does Hideez Passwordless Authentication Solution Work?


Say Goodbye to Passwords: Experience True Passwordless SSO
Regardless of how many Identity Providers you have, Hideez can assist you in getting rid of passwords. By expanding your investment in SSO and making it passwordless, you can attain the highest level of assurance for all of your applications. With Hideez, the possibilities for authentication are endless!
Streamline Your Workflow with Remote Login Solutions
With Hideez, you can equip your team with speedy and straightforward passwordless security that works on all their devices, applications, networks, and more. By using Hideez, you can streamline and consolidate logins for desktops, RDP and VDI, which can boost your team's efficiency no matter where they are working from.

Proximity-based PC Login and Unattended Logout
Our hardware security vaults store up to 2,000 passwords per device. With automatic proximity lock/unlock for PCs, you can ensure that access to your desktop computers is always secure. Our solution also provides the ability for remote user logout, allowing you to end user sessions remotely.

Seamless Integration with Cloud Based and On-Prem Services
Our access and identity management tools integrate seamlessly with Active Directory and Azure AD, providing centralized authentication with SAML SSO. Our user authentication solution supports both modern and legacy applications.
Admin Console for Managing Users and Access Rights
Our user access management tools allow you to manage authentication methods and access rights of all employees, with the ability to revoke or delete users from a central admin console. With customizable solutions, easy deployment, and support, you can manage user access with ease!
Internet Connection Is Not Required for End Users
Stay connected to your corporate resources even without an internet connection. Our passwordless authentication solution allows employees to access apps and log in to workstations offline. With our mobile app, employees can using one-time access codes, while Hideez Keys offer one-touch login with a PIN code.
CASE STUDY
Hardware Security Keys for Law Enforcement Agencies
This one-pager case study offers valuable insights into the practical applications of the Hideez Service within law enforcement agencies. Explore how Hideez can enhance your cybersecurity defenses and safeguard critical resources from unauthorized access.

FIDO U2F (Level 1) Certified
FIDO2 (Level 1) Certified

Citrix-Ready Solution
Microsoft-approved
FIDO2 Security Key Vendor
Meets NIST
Password Guidelines

AWS Marketplace Product
Choose Your Package And Start Right Now!
Start delivering the seamless, secure authentication experiences your workers are looking for

FREE Basic Identity Cloud
$2 per user/month (20 free users)
Multi-tenant IDaaS platform
Passwordless Single Sign-On (SSO)
Passwordless Multi-Factor Authentication
Admin dashboard for identity management
Custom Branding & Reporting
Integration: Azure AD and hundreds of popular web services through SAML and OIDC

Enterprise Identity
from $6 per user/month
Dedicated cloud service or on-premises deployment
Passwordless Single Sign-On (SSO)
Passwordless multi-factor authentication (MFA)
Admin dashboard for identity management
Smart endpoint authentication (Proximity-based login & logout)
Password-based authentication and TOTP
Remote access to servers and desktops
Integration: On-premises Active Directory, Azure AD, API, MS SQL, My SQL, SIEM