Passwordless Authentication and MFA Solutions

Enhance your business security with universal passwordless authentication tools! Fast and phishing-resistant access to corporate resources and workstations.
- Easy to try30-day trial (cloud deployment)
- Integrazionewith Active Directory & Entra ID
- Mercato AzureDisponibile su Microsoft Azure Marketplace
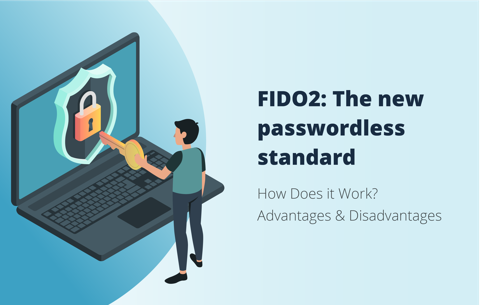
What is Passwordless Authentication?
How Will Your Organization Benefit From Passwordless Authentication and MFA?
- Improved Security: Passwords can be stolen or cracked, leaving enterprise networks vulnerable to attacks. Replace traditional passwords with stronger, more secure sign-in methods, such as biometrics or security keys.
- Reduced IT Burden: La gestione delle password richiede tempo ed è costosa per i dipartimenti IT. Le soluzioni senza password eliminano la necessità di gestire e reimpostare le password, liberando risorse IT per altre attività.
- Esperienza utente migliorata: Passwordless login streamlines the authentication process, making it more user-friendly. This, in turn, can improve employee productivity and satisfaction.
- Compliance: L'autenticazione senza password fornisce misure di autenticazione più efficaci, consentendo alle organizzazioni di conformarsi a vari requisiti normativi, come GDPR, HIPAA, PCI DSS e altri.
Come funziona la soluzione di autenticazione senza password Hideez?


Dì addio alle password: sperimenta il vero SSO senza password
Indipendentemente da quanti provider di identità possiedi, Hideez può aiutarti a sbarazzarti delle password. Ampliando il tuo investimento in SSO e rendendolo senza password, puoi ottenere il massimo livello di sicurezza per tutte le tue applicazioni. Con Hideez, le possibilità di autenticazione sono infinite!
Streamline Your Workflow with Remote Login Solutions
Con Hideez, puoi dotare il tuo team di una sicurezza senza password rapida e semplice che funziona su tutti i loro dispositivi, applicazioni, reti e altro ancora. Utilizzando Hideez, puoi semplificare e consolidare gli accessi per desktop, RDP e VDI, il che può aumentare l'efficienza del tuo team, indipendentemente da dove lavori.

Proximity-based PC Login and Unattended Logout
Le nostre casseforti di sicurezza hardware memorizzano fino a 2.000 password per dispositivo. Con il blocco/sblocco automatico di prossimità per PC, puoi garantire che l'accesso ai tuoi computer desktop sia sempre sicuro. La nostra soluzione offre inoltre la possibilità di disconnettere l'utente remoto, consentendoti di terminare le sessioni utente in remoto.

Seamless Integration with Cloud Based and On-Prem Services
I nostri strumenti di gestione degli accessi e delle identità si integrano perfettamente con Active Directory e Azure AD, fornendo autenticazione centralizzata con SAML SSO. La nostra soluzione di autenticazione utente supporta sia applicazioni moderne che legacy.
Console di amministrazione per la gestione degli utenti e dei diritti di accesso
I nostri strumenti di gestione dell'accesso degli utenti ti consentono di gestire i metodi di autenticazione e i diritti di accesso di tutti i dipendenti, con la possibilità di revocare o eliminare gli utenti da una console di amministrazione centrale. Con soluzioni personalizzabili, facilità di implementazione e supporto, puoi gestire l'accesso degli utenti con facilità!
La connessione Internet non è richiesta per gli utenti finali
Rimani connesso alle tue risorse aziendali anche senza connessione internet. La nostra soluzione di autenticazione senza password consente ai dipendenti di accedere alle app e accedere alle workstation offline. Con la nostra app mobile, i dipendenti possono utilizzare codici di accesso monouso, mentre Hideez Keys offre l'accesso one-touch con un codice PIN.
Main Components of Our Authentication Service

Plugin di identità
Azure AD
AD locale
Ping ID
Okta
One Login

ForgeRock