Active Directory im Vergleich zu LDAP. Wofür wird LDAP verwendet?
Inhalt
Für Managed Services Provider (MSPs) sind Active Directory und Lightweight Directory Access Protocol (AD und LDAP) so häufig und vertraut, dass sie selten über ihre Funktionen und die effektivste Nutzung diskutieren. Dies ist bedauerlich, da AD und LDAP für alle Arbeiten, die IT-Experten durchführen, von entscheidender Bedeutung sind. Aus diesem Grund ist es unerlässlich, dass diese Konzepte gründlich verstanden und reflektiert werden, um zu zeigen, wie sie am effektivsten innerhalb von IT-Organisationen angewendet werden können. Um dieses Verständnis zu erleichtern, haben wir beschlossen, die wichtigen Beziehungen zwischen LDAP und AD sowie einige der Hauptunterschiede zwischen ihnen zu erklären.
Active Directory und seine Dienste
Active Directory (AD) ist ein von Microsoft entwickeltes Tool zur Verwaltung von Netzwerkbenutzern, auch als Verzeichnisdienst bezeichnet. Ein Verzeichnis ist einfach eine Datenbank, die Informationen über die Benutzer eines Unternehmens enthält, einschließlich ihrer Namen, Logins, Passwörter, Titel, Profile usw.
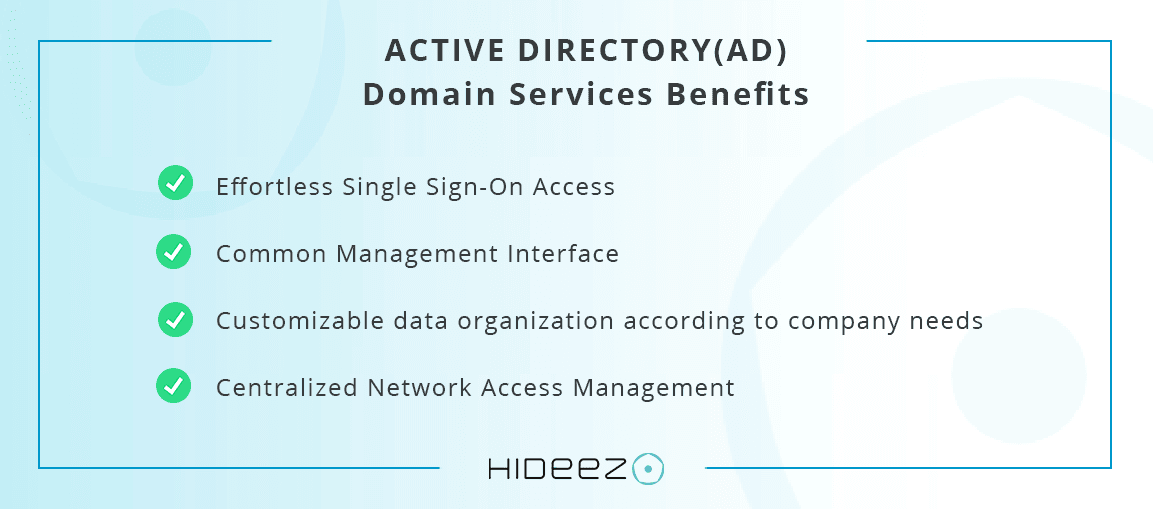
Zu den Hauptfunktionen von AD gehören:
- Zentralisierte Authentifizierung
- Kontrolliertes Sicherheitsniveau
- Unterteilung von Domänen in logische Einheiten
- Bietet Datenreplikationsmöglichkeiten
- Ermöglicht Zuweisung und Pflege mehrerer Domänen
- DNS-basierte Namenssystemvereinheitlichung
- Bietet einen Index der verfügbaren Ressourcen im Netzwerk
Wie funktioniert Active Directory (AD)?
Es gibt zwei Möglichkeiten, wie AD funktioniert.
Wie AD aus der Sicht eines Benutzers funktioniert
Aus der Sicht der Benutzer funktioniert AD so, dass sie auf die verfügbaren Ressourcen im Netzwerk zugreifen können. Sie müssen sich nur einmal in der lokalen Netzwerkumgebung anmelden, um dies zu erreichen (normalerweise beim Starten des Betriebssystems). Wenn ein Benutzer seinen Login und sein Passwort eingibt, bestimmt AD, ob die von ihnen bereitgestellten Daten gültig sind, und führt bei Bedarf eine Authentifizierung durch. Der Verzeichnisdienst von Active Directory kontrolliert dann den Zugriff auf gemeinsam genutzte Ressourcen im gesamten Firmennetzwerk.
Technische Funktionsweise von AD
Wir können verstehen, dass Active Directory (AD) als eine Datenbank (in einem Verzeichnismodell) funktioniert, die innerhalb eines Computernetzwerks, das Windows Server verwendet, eine spezifische Funktion ausführt: die Verwaltung von Netzwerkbenutzern.
Wichtige Funktionen in Active Directory Domänendiensten
Zur Koordination vernetzter Komponenten verwendet Active Directory Domänendienste eine gestaffelte Layoutstruktur aus Domänen, Bäumen und Forests. Von den Hauptstufen sind Forests die größten und Domänen die kleinsten.
In derselben Domäne befinden sich viele Objekte wie Benutzer und Geräte, die dieselbe Datenbank teilen.
Ein Baum ist eine oder eine Sammlung von Domänen mit einer Hierarchie von Vertrauensbeziehungen.
Ein Forest ist eine Sammlung mehrerer Bäume. Während Domänen, die eine gemeinsame Datenbank teilen, für Einstellungen wie Authentifizierung und Verschlüsselung konfiguriert werden können, stellt der Forest Sicherheitsgrenzen bereit.
Was ist LDAP und wofür wird LDAP verwendet?
Es ist wichtig, Daten und Benutzeranmeldeinformationen ordnungsgemäß zu verwalten, wenn es mehrere Computer in einem Netzwerk gibt. Ein System wie LDAP ist entscheidend für die Erstellung hierarchischer Strukturen. Es ermöglicht uns, die Informationen aller Geräte korrekt zu speichern, zu verwalten und zu schützen und ist auch dafür verantwortlich, alle Benutzer und Vermögenswerte zu verwalten.
Definition des Lightweight Directory Access Protocol
Lightweight Directory Access Protocol, besser bekannt als LDAP, ist ein offenes, herstellerunabhängiges, industrielles Standardanwendungsprotokoll für den Zugriff und die Verwaltung verteilter Verzeichnisdienste über ein Internet Protocol (IP) Netzwerk. Es ist auch bekannt als "Lightweight Directory Access Protocol", das ein TCP/IP-Anwendungsprotokoll ist, das den Zugriff auf einen geordneten und verteilten Verzeichnisdienst ermöglicht, um Informationen in einer Netzwerkumgebung zu suchen.
Wofür wird LDAP verwendet?
Typischerweise ist ein LDAP-Server dafür zuständig, Authentifizierungsdaten wie Login und Passwort zu speichern, die später zur Gewährung des Zugriffs auf ein anderes Protokoll oder einen anderen Systemdienst verwendet werden. Es kann mehr als nur den Login und das Passwort speichern, einschließlich der Kontaktdaten des Benutzers, des Standorts nahegelegener Netzwerkressourcen, digitaler Zertifikate für die Benutzer selbst und vieles mehr. Ohne mehrere Benutzer im Betriebssystem erstellen zu müssen, können wir über das viel flexiblere und leistungsstärkere LDAP-Zugriffsprotokoll auf die Ressourcen des lokalen Netzwerks zugreifen. LDAP ermöglicht beispielsweise Authentifizierungs- und Autorisierungsaktivitäten für Benutzer verschiedener Software, einschließlich Docker, OpenVPN, Dateiserver wie die von QNAP, Synology oder ASUSTOR und viele weitere Anwendungen. Ein LDAP-Server befindet sich typischerweise in einem privaten Netzwerk oder lokalen Netzwerk, um die verschiedenen Apps und Benutzer zu authentifizieren, obwohl er auch auf öffentlichen Netzwerken arbeiten kann.
Mit LDAP können wir auch Daten zwischen mehreren Servern austauschen. Wenn wir uns auf einem Server authentifizieren und er die benötigten Informationen nicht hat, können wir einen anderen Server im gleichen lokalen Netzwerk abfragen, um festzustellen, ob wir diese Informationen wirklich haben oder nicht. Es ist vergleichbar mit dem, was passiert, wenn DNS-Server miteinander kommunizieren, während sie den Baum hinaufgehen, bis sie die Root-Server erreichen.
LDAP für SSO
Die Verwendung sicherer und effektiver Benutzeridentifizierungssysteme ist zu einer entscheidenden Notwendigkeit geworden, da Unternehmen in Größe und Komplexität wachsen. SSO mit LDAP oder SSO unter Verwendung von LDAP ist eine derzeit stark genutzte Authentifizierungsmethode. SSO-Systeme ermöglichen den Zugriff auf eine Reihe von Systemen mit nur einer Anmeldung, wobei LDAP als das Authentifizierungsprotokoll verwendet wird, das von diesen SSO-Systemen genutzt wird.
Ein Beispiel dafür, wie LDAP genutzt wird, ist ein E-Mail-Client, der nach E-Mail-Adressen von Personen sucht, die an einem bestimmten Ort wohnen, wie einer Stadt oder sogar einem Dorf. LDAP wird nicht nur verwendet, um es den Menschen leichter zu machen, Kontaktdaten zu erhalten. Mit Problemen wie Verschlüsselungszertifikaten in Maschinen ist seine Verwendung sehr umfassend, und es durchsucht auch zusätzliche Ressourcen, die mit dem Netzwerk verbunden sind, wie Scanner und Drucker.
Der LDAP-Server kann öffentlich oder sogar kleine Arbeitsgruppenserver sein. Wie bei anderen Servern legt der Administrator die Berechtigungen fest, die für diese Datenbanken erlaubt sind.
SSO steht andererseits für Single Sign-On und ist eine Lösung, die es einem Benutzer ermöglicht, sich nur einmal anzumelden, um auf zahlreiche Systeme zuzugreifen. Die vielen Systeme, die Teil des Benutzersystems sind, erfordern keine zusätzlichen Anmeldeaufforderungen. Die Verwendung des SSO-Systems bietet bessere Sicherheit und reduzierte Phishing-Aktivitäten als ihre wichtigsten Vorteile. Die geringeren Authentifizierungsversuche sind ebenfalls ermutigend, da sie verhindern, dass Endbenutzer Passwortmüdigkeit bekommen. Dies führt zu geringeren Kosten für den Betrieb des Helpdesks.
Betrachten wir diese beiden Anwendungen, ist der Unterschied, über den diskutiert werden kann, dass LDAP ein Anwendungsprotokoll ist, das verwendet wird, um Daten auf der Serverseite zu überprüfen. SSO verwendet jedoch die Benutzerauthentifizierung, wobei der Benutzer Zugang zu mehreren Systemen erhält.
Active Directory vs LDAP
AD und LDAP können zusammenarbeiten, um die Sicherheit der Unternehmen insgesamt zu verbessern, haben jedoch unterschiedliche Philosophien, Funktionalitäten und Standards.
Zunächst einmal ist LDAP ein offenes Anwendungsprotokoll, das außerhalb des Windows-Frameworks arbeitet und hauptsächlich auf Unix- und Linux-Umgebungen abzielt. Andererseits ist AD Microsofts proprietäre Lösung für den Zugriff und die Organisation von Verzeichnissen.
Zweitens ist LDAP ein grundlegendes Protokoll, das mit Verzeichnisdienstanbietern wie Active Directory, Red Hat Directory Server, OpenLDAP und IBM Security Directory Server kompatibel ist. Benutzer können es verwenden, um Elemente in Verzeichnissen zu suchen und zu ändern. Auf der anderen Seite ist AD hauptsächlich eine Verzeichnisdienstimplementierung mit Funktionen wie Gruppen- und Benutzerverwaltung, Richtlinienverwaltung und Authentifizierung.
Drittens, da LDAP eine Open-Source-Lösung ist, unterscheidet es sich konzeptionell von SSO. Das AD unterstützt jedoch Domänen und SSO. Wenn beispielsweise das Netzwerkbetriebssystem (NOS) mehrere AD-Domänen enthält, können Sie SSO auf Clients konfigurieren, um über Domänen hinweg zu arbeiten.
Schließlich ist Active Directory eine der Lösungen, die Dienste bereitstellen kann, die LDAP nutzen. LDAP ist andererseits ein Protokoll und wird häufiger verwendet als Active Directory. Sie werden höchstwahrscheinlich LDAP verwenden, egal ob Sie Active Directory, OpenLDAP oder jeden anderen von anderen Unternehmen bereitgestellten Verzeichnisdienst verwenden.
Verwendet Active Directory LDAP?
Obwohl LDAP und AD nicht gleichwertig sind, können sie einander ergänzen, zum Vorteil Ihres Unternehmens oder Ihrer Organisation. AD ist ein Verzeichnisdienst für Microsoft, der wichtige Informationen über Personen innerhalb einer bestimmten Organisation auf eingeschränkter Basis zugänglich macht. LDAP ist hingegen ein Protokoll, das nicht nur von Microsoft verwendet wird und es Benutzern ermöglicht, ein AD zu durchsuchen und den Zugriff darauf zu authentifizieren.
Einfach ausgedrückt ist LDAP eine Möglichkeit, mit Active Directory zu kommunizieren. Es ist ein Protokoll, das von vielen verschiedenen Verzeichnisdiensten verstanden werden kann, daher ist es ein Verzeichnisdienstprotokoll. Während Active Directory ein Verzeichnisserver ist, der das LDAP-Protokoll verwendet.
In dieser modernen Zeit, in der die digitale Sicherheit niemals umfassend genug sein kann, ist es unmöglich, die Bedeutung von IT-Experten zu betonen, die diese Konzepte verstehen und auf Weisen anwenden, die für ihr Geschäft geeignet sind.
Zuverlässiger Schutz für Ihre AD-Umgebung
Seit 12 Jahren beschäftigt sich unser Unternehmen mit der Lösung komplexer Probleme für Unternehmenskunden mit einer einfachen Mission. "Wir entwickeln zuverlässige und bequeme Identitäts- und Zugriffsverwaltungslösungen". Seitdem haben wir positive Bewertungen von Centrify, CyberArch, Cyphort, ISACA, Arzinger, Saife usw. erhalten.
Hideez Authentication Service konsolidiert alle vorhandenen Authentifizierungsmethoden - Passwörter, Einmalpasswörter, starke Zwei-Faktor-Authentifizierung (FIDO U2F), passwortlose Authentifizierung (FIDO2) und Single Sign-On (SSO) in einer Lösung, die sich problemlos in die Enterprise-Umgebung integrieren lässt, basierend auf den Fähigkeiten zur Integration von Hideez Enterprise Server mit LDAP und SAML. Ihr IT-Team kann Zeit und Kosten sparen und sicherstellen, dass alle Benutzer sicher authentifiziert werden und nur auf das zugreifen, was erlaubt ist.
Weitere Informationen erhalten Sie durch die Planung einer persönlichen Demo und erfahren, wie Hideez dazu beitragen kann, Ihre Active Directory / Azure Active Directory-Umgebung zu schützen.
Oleksii Leonov ist Experte für föderierte Identitäten, Zugriffskontrolle und moderne Authentifizierungsstandards. Er ist spezialisiert auf Single Sign-On (SSO), Identitätsanbieter und Protokolle wie SAML und OIDC und hilft Unternehmen dabei, die Sicherheit zu verbessern und Authentifizierungsprozesse zu optimieren.




