Multi-Faktor-Authentifizierung: Warum ist ein separates tragbares Gerät besser als Ihr Smartphone?
In den Vereinigten Staaten haben etwa 19% der erwachsenen Bevölkerung Identitätsdiebstahl erlebt. Über 60 Millionen Amerikaner hatten ihre Online-Identität durch Hacks der Kundendatenbanken ihrer Dienstleister oder Regierungsbehörden ausgesetzt. Die Situation ist in Europa und anderen Ländern ähnlich.
Identitätsdiebstahl ist nicht das einzige Verbrechen, das mit gehackten Passwörtern und kompromittierten Online-Konten einhergeht: Kreditkartenbetrug, Erpressung, Privatsphärenverletzungen und illegales Abhören kommen weltweit häufig vor.
Multi-Faktor-Authentifizierung (MFA, manchmal vereinfacht als ‚Zwei-Faktor‘ oder 2FA) hat sich als wirksames Mittel zur Verbesserung der Sicherheit von Online-Konten erwiesen. Das Aktivieren von MFA oder 2FA bedeutet jedoch nicht automatisch, dass Ihr Konto sicher ist.
Das Militär und die Elite haben MFA seit Jahrhunderten verwendet. Zum Beispiel erhält d'Artagnan in den „Drei Musketieren“ von Alexandre Dumas einen Ring von Königin Anne von Frankreich zusätzlich zu den mündlichen Anweisungen, die er benötigt, um dem Herzog von Buckingham zu warnen, dass Kardinal Richelieu und Milady de Winter planen, ihn zu töten.
Die moderne Nutzung von MFA zur Sicherung von Computeraufzeichnungen und Online-Konten stammt aus dem Bankensektor, wobei das typische Beispiel die Geldabhebung an einem Geldautomaten ist, die eine Bankkarte besitzen und die PIN kennen erfordert.

Person am Geldautomaten. Bild von Pixabay
Anfang der 2000er Jahre führten Banken, Online-Shops und Dienste eine Telekom-Version von 2FA ein, die auf SMS mit einem Einmalpasswort (OTP) basiert. Jetzt ist dies synonym mit 2FA selbst.
Kürzlich haben mobile Anwendungen (z.B. plattformübergreifender Google Authenticator) 2FA unabhängig von Mobilfunkanbietern auf mobile Plattformen gebracht, indem sie TOTP und HMAC Software-Algorithmen verwenden.
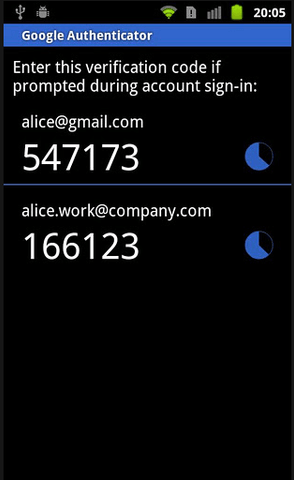
Screenshot von Google Authenticator auf Android-Smartphone. Bild von AskUbuntu über StackExchange
Warum sollte man sich also noch mit altmodischen Hardware-Authentifizierungstokens abmühen, die erfordern, dass man noch ein weiteres Objekt mit sich herumträgt?
In diesem Beitrag werden wir versuchen zu erklären, warum eine Hardware-Zweifaktor-Lösung eine gute Option ist und führen Sie durch die Funktionen unseres Flaggschiffprodukts, des Hideez Key, das Hardware-MFA zu einer effektiven und benutzerfreundlichen Lösung für solche Fälle macht.
Ein externes Gerät ist ein wahrer zweiter Faktor, in der Tat — einer der vielen Faktoren, die erforderlich sind, um sich im modernen Cyberspace sicher zu fühlen
In Zeiten, in denen Online-Kriminelle und Regierungen sogar die Zwei-Faktor-Authentifizierung umgehen können, ist es keine gute Lösung, den zweiten Faktor demselben Gerät anzuvertrauen, das Sie schützen möchten. Die bekannten drei Säulen der Zwei-Faktor-Authentifizierung sind was Sie wissen (d.h. Passwort oder PIN), was Sie haben (d.h. Bankkarte, digitales Token oder ein anderer physischer Gegenstand) und was Sie sind (d.h. biometrische Daten wie Fingerabdrücke, Iris- oder Augenvenen, die Art und Weise, wie Sie auf Ihrer Tastatur tippen, Schallwellenmuster Ihrer Stimme oder Ihres Herzschlags, etc.).
Kunden, die nur softwarebasierte 2FA verwenden, beschränken sich auf das, was sie wissen, d.h. ihr dauerhaftes Passwort oder ihre Passphrase und ein Einmalpasswort (OTP) oder eine PIN, die letztendlich nur ein weiteres Passwort ist. Dies bedeutet, dass ein Computerfachmann oder Krimineller, der irgendwie die Kontrolle über Ihr Client-Gerät erlangt oder die Möglichkeit hat, zu sehen, was auf Ihrem Bildschirm ist (denken Sie an CCTV oder versteckte Überwachungskameras in modernen Bürogebäuden), softwarebasierte 2FA auf diese Weise umgehen kann.
Angesichts aller Bedrohungen der modernen Welt empfehlen wir unseren Kunden tatsächlich, über herkömmliche 2FA hinauszugehen und komplexere MFA mit biometrischen Daten als primärem Faktor für die Authentifizierung zu nutzen, wobei alle anderen Hilfsfaktoren nur erforderlich sind, um die Authentizität der auf den biometrischen Daten basierenden Bestätigungsnachricht zu beweisen. Hier beginnt die Benutzerfreundlichkeit eine Schlüsselrolle zu spielen.
Richtig eingerichtet und verwendet, können externe Geräte zuverlässiger sein als OTP
Seit Ende der 2000er Jahre sind per SMS übermittelte OTPs zu einer sehr beliebten Authentifizierungsmethode geworden, da sie billiger zu implementieren sind und Benutzer an mobile Geräte gewöhnt sind. Dies erhöht das Bewusstsein für 2FA und die Zugänglichkeit, was gut ist. Dennoch sind OTP-SMS eine weniger sichere Lösung als Hardware-Authentifizierungsgeräte.
Derzeit bevorzugen 56% der Unternehmen OTP-SMS für MFA. Leider ist dies keine besonders zuverlässige Methode, um Konten zu schützen. Hacker wissen, wie sie OTP-SMS abfangen können, indem sie gefälschte Basisstationen oder Wi-Fi-Hotspots verwenden, die den Verkehr in die Mobilfunknetze ihrer Opfer umleiten.
Hacker und sogar Regierungsbeamte, die sich um die Sicherheit ihrer VIPs kümmern, wissen auch, dass Hardware-Authentifizierungstokens schwieriger zu hacken sind, als man denkt, wenn man bedenkt, dass die Token selbst geheim sind (sie sind nicht mit dem Internet verbunden und verwenden drahtlose Schnittstellen wie Bluetooth oder Near Field Communication nur dann, wenn sie während der Authentifizierung an das Mobilgerät oder einen speziellen USB-Dongle angeschlossen werden).
Unter der Annahme, dass ein Hideez Key für Hardware-MFA verwendet wird, wenn ein Konto versucht wird zu authentifizieren, wird das Gerät für einen bestimmten Zeitraum, z.B. 30 Sekunden, aktiviert und ist die einzige Möglichkeit, sich für diesen Zeitraum zu authentifizieren. Wenn die Anfrage nicht rechtzeitig beantwortet wird, wird die Authentifizierungsanforderung storniert, und das Gerät wird deaktiviert, was die Möglichkeit von Fehlern oder Hacks weiter reduziert.
Der Hideez Key wurde entwickelt, um Hardware-Zweifaktor-Lösungen einfach und zugänglich zu machen. Es sieht aus wie ein regulärer Autoschlüsselanhänger und kann sich in Ihrem Taschen- oder Rucksackschlüsselanhänger einfügen. Es ist extrem leicht und einfach zu bedienen.
Hideez Key kann Passwörter und Schlüssel speichern, eine Funktion von HID-Tokens, die wir schon früher erwähnt haben, und kann automatisch Daten für den autorisierten Benutzer eingeben. Hideez Key kann auch verwendet werden, um Online-Konten mit Yubikey-ähnlichen FIDO2-Anmeldeinformationen zu sichern, die für die vollständige passwortlose Authentifizierung bei Online-Diensten wie Google, Facebook, Twitter und vielen anderen verwendet werden können. Sie können die Option auf den Unterstützungsseiten dieser Dienste überprüfen.
Zusammengefasst bieten Hardware-Authentifizierungsgeräte eine sicherere und robustere Lösung zur Sicherung Ihrer digitalen Identität und Daten, insbesondere wenn sie in einer immer vernetzteren Welt korrekt eingerichtet und verwendet werden. Für weitere Informationen zu den Funktionen und Vorteilen der Hideez Key besuchen Sie bitte die Produktseite.
Oleg Naumenko ist CEO und Gründer von Hideez. Er ist spezialisiert auf passwortlose Authentifizierung, FIDO2-Schlüssel und Zugriffsverwaltungslösungen. Dank seiner umfassenden Erfahrung im Bereich Informationssicherheit unterstützt Oleg Unternehmen bei der Umstellung auf eine passwortlose, Phishing-resistente Mitarbeiterauthentifizierung.



